
There is a moment that every business owner dreads — but rarely prepares for correctly.
It is 2:30 in the morning. Your jewellery showroom sits empty on a busy commercial street in Surat. Three men cut through the rear shutter. Your alarm triggers. A notification fires to your mobile phone.
Your phone is on silent.
By the time your sleep-addled brain registers the vibration — if it does at all — the men are gone. Bags packed. Display cases shattered. And in September 2023, a similar scenario played out at Umrao Singh Jewellers in Delhi, where thieves broke through a showroom between Sunday night and Monday, disabled all six CCTV cameras, and walked away with over ₹20 crore in gold and diamond jewellery. The showroom had no dedicated night guard — only a shared common guard from the market. Many such incidents involve alarm systems that trigger but fail to generate effective response, because the gap between detection and action is never closed.
This is the central problem with modern alarm systems in India: the alarm works. The response fails.
According to the National Crime Records Bureau’s 2023 Crime in India report, property offences across the country rose 4.7%, recording 1,07,573 burglary cases. More strikingly, of the ₹6,917 crore worth of property stolen in 2023, only ₹2,065 crore — a mere 29.9% — was ever recovered. That means more than 70% of stolen property is simply gone. Forever. The alarm went off. Nobody stopped it.
The question Indian businesses must now ask is not “Do I have an alarm system?” but rather: “What happens when that alarm triggers at 2 AM — and who is responsible for the response?”
The answer to that question is what separates a notification from protection.
Modern alarm systems are engineering marvels. PIR sensors, door-breach detectors, smoke triggers, and panic buttons communicate instantly over cellular and Wi-Fi networks to mobile apps. When an event occurs, a push notification reaches a phone within seconds.
But a notification is not a response. It is an invitation to respond.
And that invitation goes unanswered far more often than businesses realise.
Research on alert behaviour across security operations reveals a deeply uncomfortable pattern. Studies from cybersecurity monitoring where the problem is well-documented show that alert fatigue causes a significant percentage of alerts to be ignored or dismissed without investigation. An IDC white paper cited by Proofpoint found that up to 30% of security alerts in operations centres go uninvestigated. Atlassian’s research found that 52% of alerts are false positives and 64% are redundant — a combination that trains human beings, across security contexts, to treat alarms as background noise over time.
While these findings originate in digital security operations, the underlying human behavioural dynamic — that repeated, unactionable alerts erode response urgency applies with equal force to physical alarm notifications sent to a business owner’s mobile phone.
This phenomenon is called alert fatigue and it is as real in physical security as it is in cyber operations.
When a store owner receives a motion alert at 1 AM for the third Tuesday in a row because the cleaning staff triggered a sensor, the fourth alert — the real one — gets the same cognitive response as the first three: a brief glance, a dismissal, a return to sleep. This is not negligence. It is human nature, documented and predictable.
The consequence in physical security terms is stark: the alarm fires, the alert goes to mobile, and the thief who has already done three nights of reconnaissance has approximately 7 to 12 minutes before anyone physically responds. For a jewellery showroom, a mobile store, or a bank branch with a cash safe, 7 minutes is not a window. It is a heist.
The terminology matters here, because it shapes how business owners budget, plan, and ultimately protect themselves.
An alarm notification is a signal sent to a person. What happens next depends entirely on whether that person sees it, interprets it correctly, knows what to do about it, and has the ability to act. There is no guarantee of response. No documented protocol. No escalation path if the primary contact is unavailable. No record of what was done or when.
A professional protection platform is a managed response system. When an alarm event occurs, it is received, validated, and acted upon by trained human professionals operating within a structured protocol — regardless of whether the business owner is asleep, in a meeting, or travelling abroad. Response is not an option; it is an obligation, backed by a service level agreement.
| Basic Alarm + App Notification | Professional Protection Platform |
|---|---|
| Alert sent to mobile phone | Event received and validated by monitoring centre |
| Owner responsible for response | Trained Protection Officer responds within 60 seconds |
| No guaranteed action | SLA-backed escalation protocol |
| No documentation | Audit-ready incident logs and reports |
| Reactive — you act if you see it | Actively supervised — professionals act regardless |
| Response depends on one person | Structured escalation across multiple contacts |
| No system health tracking | Monthly remote health verification |
This is the foundational shift that Indian businesses particularly in high-risk verticals like jewellery retail, banking, warehousing, and electronics must make in how they think about security investment.
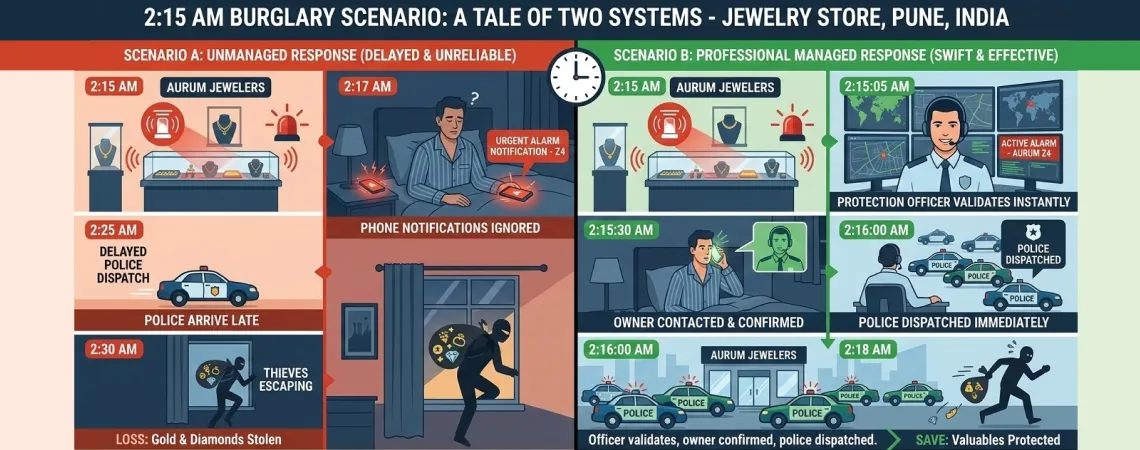
Abstract comparisons rarely persuade. Let us make this concrete.
The Scenario: A jewellery showroom in Pune. Wednesday night, 2:15 AM. Three individuals have used an adjacent building’s roof access to reach a rear window. One has disabled the exterior CCTV camera with spray paint. The motion sensor inside the display area is triggered as the first man enters.
The difference is not technology. Both scenarios had the same sensor, the same alarm panel. The difference is what happened in the 60 seconds after the signal was received.
Industry benchmarks bear this out. Underwriters Laboratories (UL) — the global benchmark for alarm monitoring quality — defines operator response expectations and staffing requirements for certified central monitoring stations under UL 827. In practice, many professional monitoring stations operate with response benchmarks of around 60 seconds or less, with the better-run centres processing and initiating escalation in under 15 seconds from signal receipt.
In security events, this is not a marginal improvement. It is the difference between prevention and loss.
Security professionals have long understood what general business owners are only beginning to appreciate: response latency determines loss severity.
In the context of commercial burglary, organised theft operations in India are increasingly systematic. The Karnataka State Bank of India robbery uncovered in 2024 revealed that a criminal gang had planned and rehearsed their approach for over six months — studying bank schedules, staff routines, and most critically, how long it would take for anyone to respond after an alarm. They counted on the gap. They built their operation around it.
A 60-second SLA-backed response from a professional monitoring centre fundamentally disrupts that calculation. The criminal’s assumption — that an alarm means nothing will happen for 10 to 20 minutes — is invalidated from the first second of breach.
For high-value business environments, this shift in criminal calculus is the primary security benefit. A protected premises where alarms trigger immediate, structured, documented response is not worth the risk. An unmonitored premises where alarms send silent notifications to sleeping phones is an invitation.
Speed determines intervention possibility. Faster escalation to emergency services — with verified event details and precise location — significantly increases the chances of timely intervention. Every minute of delay between alarm trigger and police dispatch reduces the probability of catching perpetrators before they exit the area.
Validation eliminates hesitation. A trained Protection Officer who validates an event before escalating ensures that responders act with confidence — not confusion. When police receive a verified emergency signal rather than an owner’s uncertain “I think my alarm went off,” they respond differently.
Documentation creates accountability. Every step in a professional escalation protocol is timestamped and logged. This creates the incident record that insurers require, that compliance auditors examine, and that investigators use. A silent app notification creates no such record.
The technology debate in security has been dominated, for years, by a false binary: cameras versus sensors, cloud versus on-premise, AI versus manual. These are important questions. But they miss a more fundamental one: who is responsible for response?
Most alarm systems — including technologically sophisticated ones — answer this question with silence. The system detects. The system notifies. And then the system waits.
A Professional Protection Platform inserts a trained human professional into that silence.
Emergency response officers in a professional central monitoring centre are not passive message-forwarders. They are trained to:
This human layer is what transforms an alarm system from a detection tool into a protection system. Detection without response is observation. Protection requires response — structured, accountable, and fast.
The adoption of professional monitoring in India is being driven by several converging forces — some economic, some regulatory, and some simply born of painful experience.
Organised crime is more sophisticated. The incidents documented across India’s jewellery retail, banking, and warehousing sectors in recent years reveal a disturbing pattern of planning and reconnaissance. Criminal groups study response gaps. They target locations where alarms send notifications but generate no action. The rise of organised retail crime means that passive notification systems no longer represent adequate deterrence.
Multi-site operations require centralised governance. A retail chain with 8 branches, a bank with 12 NBFC locations, or a logistics company with 4 warehouses cannot rely on individual branch managers to interpret alarm notifications at 3 AM. These organisations need a centralised function that monitors all sites, responds to any event, and documents every incident. This is precisely what professional protection platforms provide.
Insurance requirements are evolving. Commercial insurers operating in India are beginning to require documented incident response procedures as conditions of coverage — particularly for high-value contents in jewellery, electronics, and financial service environments. An app-based notification system generates no documentation. A professional monitoring centre generates audit-ready incident logs for every triggered event.
Compliance demands are increasing. Organisations in banking, financial services, data management, and healthcare are subject to regulatory requirements around security governance. Professional protection platforms — with their compliance logging, fire drill documentation, system health reporting, and role-based access control — provide the structured audit trail that regulators expect.
The cost of incidents dwarfs the cost of protection. The ₹20 crore Delhi jewellery theft. The ₹1.25 crore Surat showroom heist that occurred between 5 AM and dawn. The ₹17.7 kg gold robbery at a Karnataka SBI branch during a long weekend. In every case, the property lost far exceeded any reasonable annual investment in professional monitoring. The question is not whether monitored protection is affordable. The question is whether unmonitored exposure is.
Certain business environments carry inherently elevated risk profiles that make the gap between notification and professional protection particularly consequential.
After-hours intrusion is the defining threat. India’s gold and diamond retail sector carries enormous concentrated value in relatively small physical spaces. The window between closure and opening — typically 10 to 14 hours — is precisely when organised burglary groups operate. Professional monitoring ensures that the moment any sensor within that window triggers, a trained officer is engaged within 60 seconds. No sleep, no silence, no delay.
Electronics retail faces a distinct threat profile: sophisticated theft groups who understand the high resale liquidity of smartphones, laptops, and accessories. These items are targeted specifically because they are easily fenced before any morning discovery. Professional monitoring with validated response compresses the intervention window that these operations depend on.
The regulatory and compliance dimension in financial services is substantial. Branch security incidents require documented incident reports, timestamped response records, and structured escalation evidence. Beyond compliance, the physical threat to cash safes, ATM infrastructure, and customer data makes professional monitoring a governance imperative, not merely an operational convenience.
Warehouses present a unique vulnerability: enormous perimeter, high-value contents, minimal after-hours human presence, and typically remote locations that slow police response. Professional monitoring that validates intrusion events and initiates multi-party escalation immediately after breach provides the only viable response capability for sites where no human presence exists between shifts.
Multi-location retailers face a monitoring problem that app-based systems cannot solve: a single event at one branch can be missed by a distracted area manager, ignored as a false alarm, or simply not noticed. Centralised professional monitoring provides uniform response capability across all locations simultaneously, with a single operational standard rather than 8 different people making 8 different judgment calls at 3 AM.
Physical security at technology infrastructure sites intersects directly with cyber security posture. Unauthorised physical access to server rooms, network equipment, or power infrastructure can have cascading digital consequences. Professional protection for these facilities must include structured documentation, compliance logging, and role-based access governance — precisely the features that distinguish professional platforms from passive notification systems.
A fully implemented Professional Protection Platform delivers value beyond the emergency response moment. It creates an ongoing operational infrastructure for security governance.
Monthly system health verification ensures that every component of the alarm infrastructure — sensors, panels, communication pathways, backup power — is functioning correctly. The silent failure of a sensor or a communication pathway can create an undetected gap in protection that exists for weeks or months before anyone notices. Remote health monitoring catches these failures before they matter.
Compliance and drill logging — structured documentation of fire drills, security procedure checks, and access events — provides organisations with the audit trail required by insurers, regulators, and internal governance functions. This is not paperwork for its own sake; it is the documented evidence that your security program operates as claimed.
Role-based access control with multi-user management ensures that the right people have the right level of visibility and authority over the security infrastructure. Up to 10 users across an organisation can be managed with specific permissions — protecting against both external threats and internal misuse.
Extended warranty continuity tied to an active protection plan means that the hardware investment in the alarm infrastructure is protected by ongoing warranty coverage — eliminating the scenario where a sensor fails out of warranty and an organisation delays replacement due to cost.
These governance features collectively transform a security system from a reactive device into a managed operational asset — one that generates documentation, enforces compliance, and supports business continuity.
The alarm industry in India is at an inflection point.
India’s electronic security market was valued at USD 2.42 billion in 2024 and is projected to grow at a compound annual growth rate of 23.57% to reach USD 9.11 billion by 2030, according to Mordor Intelligence — making it one of the fastest-growing security markets globally. This growth is being driven not by hardware sales alone, but by the rising understanding that detection without managed response is an incomplete solution.
Globally, the alarm monitoring market was valued at USD 65 billion in 2025, with services — professional monitoring subscriptions, compliance platforms, managed response — growing faster than hardware. The pivot is clear: businesses are no longer buying alarms. They are buying protection.
Alarm systems were designed to detect events. The next era of security requires systems that also manage response — with professional human oversight, structured escalation protocols, documented accountability, and the speed to matter.
The gap between notification and protection has always existed. What has changed is that businesses can no longer afford to pretend it doesn’t.
When a critical event occurs at your premises at 2 AM, a notification on your phone is a promise that something has gone wrong. A Professional Protection Platform is a promise that something will be done about it — within 60 seconds, by a trained professional, with a documented response protocol and a compliance-ready incident record.
That is the difference between an alarm system and protection.
Ask yourself these five questions:
If any of these questions do not have a clear, documented answer, your security program has a gap that a notification system cannot close.
Atigo’s Professional Protection Plan is designed specifically to address this gap — combining AIoT alarm infrastructure with 24/7 central monitoring, 60-second SLA-backed human response, structured escalation workflows, compliance documentation, and monthly system health verification.
If any of these questions do not have a clear, documented answer, your security program has a gap that a notification system cannot close.
or contact our team to understand how SLA-backed alarm monitoring works for your specific business environment
Atigo Smart Security has been building and monitoring India’s critical safety infrastructure since 2013, with 10,000+ active installations across the country. Atigo’s Professional Protection Plan is SLA-backed, compliance-ready monitored protection — purpose-built for Indian businesses.
India’s trusted security partner since 2013. Made in India manufacturer of 24/7 monitored alarm systems.
© 2013-2025 Atigo Security — A division of Atigo Enterprises Limited
Made in India. Monitored in India.